LUKS stands for Linux Unified Key Setup. It is an encryption specification that was written for Linux systems in 2004. LUKS is used to encrypt block devices and partitions. This encryption helps to keep our data safe in rest.

The Ghost Operator's Signal
LUKS stands for Linux Unified Key Setup. It is an encryption specification that was written for Linux systems in 2004. LUKS is used to encrypt block devices and partitions. This encryption helps to keep our data safe in rest.

It is just a quick survival guide to NMAP commands without investigating the rabbit hole of live host discovery, port scanning and firewall evasion techniques.
Continue reading “Basic NMAP commands survival guide”There are excellent Linux distributions for Cyber Security professionals like Kali. They ship all the the bells and whistles that is needed for the tasks. If we want to learn how to put together our own Penetration Testing system we can use a fresh Debian Linux box. I created a small setup from the NetInstall iso starting from the defaults.
Continue reading “How to install a Debian Linux Penetration Testing machine?”As we just dipped our pinky into 2023 the articles about Cyber Security in 2023 started to pop up on the internet. Some of them are exploring the the field as a career path and others talk about the new threats and vulnerabilities. I will review what I see about these topics.

Here is the winter holiday season and a lot of people travel and use apartments, hotel rooms, AirBNB etc. Hidden cameras and sound recording devices are small and stealthy. There is no way to be 100% sure that our room is not “wired”, but we can look around in the network if we use it and investigate our surroundings.
Continue reading “How to check the accommodation for hidden devices”The UNIX/Linux systems have a powerful tool for scheduling tasks while the computer is running. The daemon that is responsible for initiating the tasks (called cronjobs) is called cron, while the tool that lets us edit the configuration is the crontab. Once we understand the basics of cron we can easily master editing the cron files.
Continue reading “Understanding the Linux Cron and Crontab”If we installed a Debian WSL distro on our computer, there is a chance that in 6-9 months a new release will come out. We want to keep our system updated, so a distribution upgrade should happen in our WSL ecosystem.
Continue reading “How to upgrade to Debian Bullseye from Buster in WSL?”Linux supports multiple users and groups on the system to log in, create, modify and delete files and folders. System files and folders must be protected from the ordinary users to avoid accidental deletion or modification. Configuration files can contain sensitive data like passwords and certificates. Our home user directory can contain our private secrets as well. In UNIX/Linux there is a permission and owner/group system in place.
Continue reading “Understanding the Linux file permissions”TryHackMe is a great site to learn Cyber Security with practical lab exercises. I just finished their penetration tester path to refresh my knowledge.
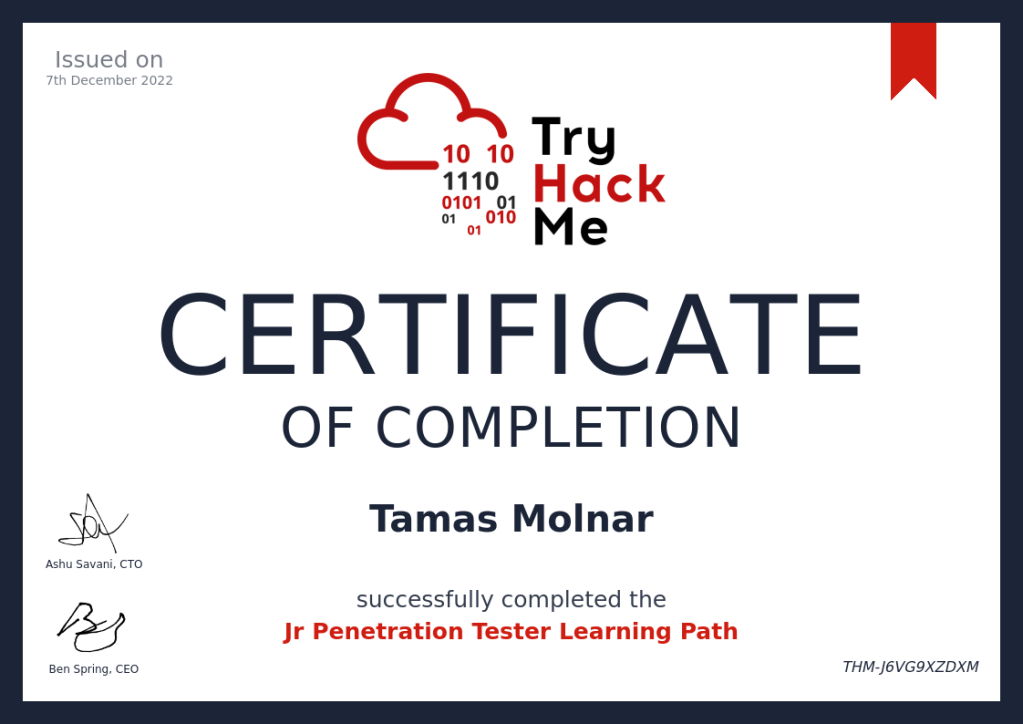
They provide a nice certificate after finishing the path and a short “test”.
2022 was a busy year for the IT professionals with the defense against the increased number of security threats. As the world has been hit by COVID-19, and many companies introduced a remote work scheme, the attack surface grew exponentially. Most companies stayed with the hybrid work model after the lockdowns, so the issue will remain with us, IT professionals to adapt to the new world.
Remote work and the “Bring Your Own Device” culture added a new level of complexity to the Cyber Defenses. More complex endpoint security and extended policies are necessary to keep up with the increased threats. Remote access and the outdated identity and access management bring huge problems into the mix.
Cyber Security starts on a personal level. It means that our professional lives are mixing our private ones, the border is blurry, not to mention that most people use their system with privileged access (as an Administrator).
Malicious actors try to get valuable information from employees of the companies even in their private life, and they try to use it later in their acts.
Here are some of my advice to stay safe(r) in 2023.
Continue reading “How to stay safe on the internet in 2023?”A lot of people are talking about the future of the IT, the traditional operations work, and they are trying to guess whether they will have a job in IT in the future.
As I see most IT colleagues feel some uncertainty about their jobs. Different positions (and position names) come and go at the huge tech, telco and financial companies. The fluctuation of the people is also constant.
Do you think your job is in danger? Read further!
Continue reading “The future of DevOps”I’ve been using the Keepass password vault for years. I don’t remember when I started to keep my secrets in it, but it can be easily a decade ago. Though I always liked Keepass, and its features are strong, times have changed and I looked for something fresher and more elegant. My choice is KeepassXC. Read more to see why!
Continue reading “Password Manager upgrade: I switched to KeepassXC”